Imagine that you need to send a message to someone. However, you do not know where he is or what his contact detail is. You just know another man who has his contacts that can send your message to him. Internet was designed in a way like the one describe above. The data passes through multiple nodes in the network to reach its destination. By the default, data will be a text plain and insecure. Any nodes, which you pass the message to get package to, can read these messages.
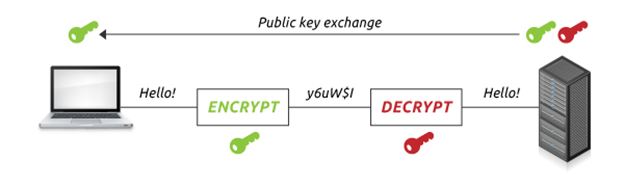
SSL and TLS are the protocols to reduce this risk. So only message owner can read message and make sure that message sender is the true person that should be. SSL and TLS are standard security protocols for establishing an encrypted communication between a server and a client.
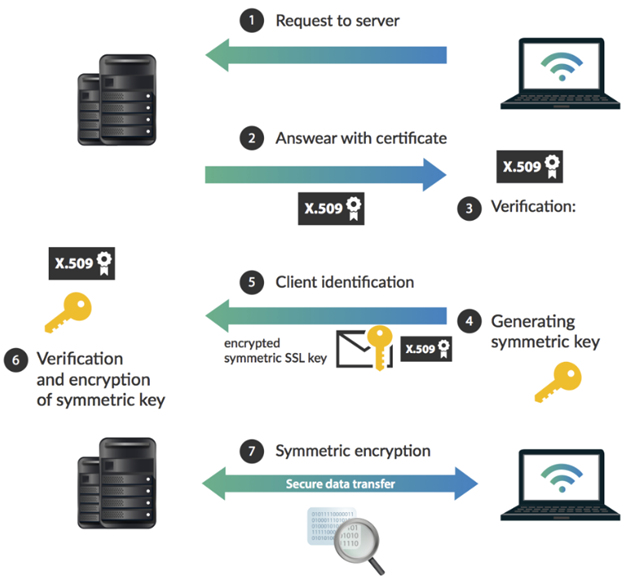
I added a simple flow how SSL and TLS connection establish between client and server. At this flow, the key point is symmetric key exchange step.
- Client and Server agree on a common ciphers which both side are supported.
- Client uses server’s public key to create encrypted symmetric key with supported ciphers and parameters.
- Server uses its private key to decrypt the symmetric key and it uses to protect session.
An SSL Certificate (.cer, .crt) is a digital file that has two-specific purpose.
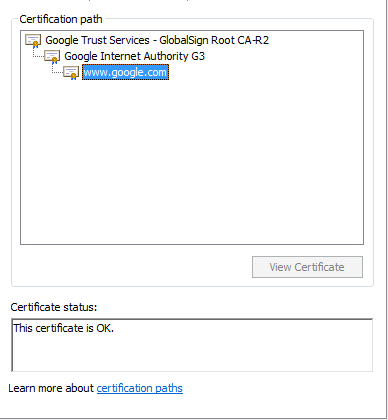
1. Authentication and Verification: The SSL Certificate has information that identify of host or site. When you check certificate chain, you should probably get who issued certificate and where it can be used.
2. Data Encryption: The SSL Certificate main purpose is data encryption, which means that all sensitive information will be encrypted between server and client.